Try Hack Me/Mouse Trap
Try Hack Me / Mouse Trap
by: alfreddgreat
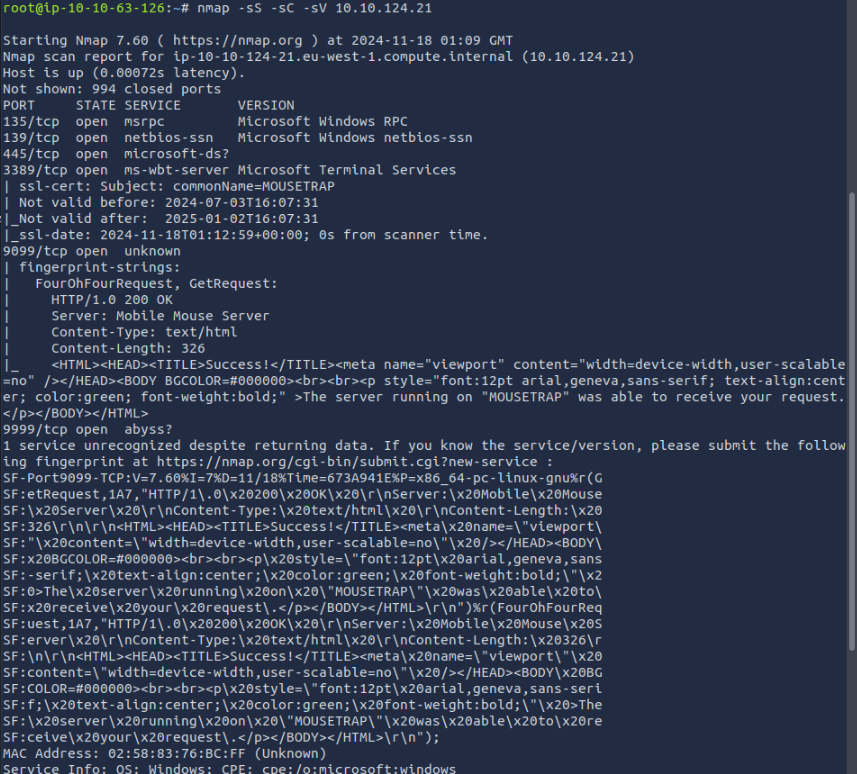
root@ip-10-10-63-126:123-135:~# nmap -sS -sC -sV 10.10.124.21162.0
root@ip-10-10-123-135:~# nmap -sS -sC -sV 10.10.162.0
Starting Nmap 7.80 ( https://nmap.org ) at 2025-03-30 22:05 BST
Nmap scan report for 10.10.162.0
Host is up (0.00028s latency).
Not shown: 994 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: MOUSETRAP
| NetBIOS_Domain_Name: MOUSETRAP
| NetBIOS_Computer_Name: MOUSETRAP
| DNS_Domain_Name: MOUSETRAP
| DNS_Computer_Name: MOUSETRAP
| Product_Version: 10.0.17763
|_ System_Time: 2025-03-30T21:08:26+00:00
| ssl-cert: Subject: commonName=MOUSETRAP
| Not valid before: 2024-12-08T13:53:36
|_Not valid after: 2025-06-09T13:53:36
|_ssl-date: 2025-03-30T21:08:54+00:00; 0s from scanner time.
9099/tcp open unknown
| fingerprint-strings:
| FourOhFourRequest, GetRequest, ms-sql-s:
| HTTP/1.0 200 OK
| Server: Mobile Mouse Server
| Content-Type: text/html
| Content-Length: 326
|_ <HTML><HEAD><TITLE>Success!</TITLE><meta name="viewport" content="width=device-width,user-scalable=no" /></HEAD><BODY BGCOLOR=#000000><br><br><p style="font:12pt arial,geneva,sans-serif; text-align:center; color:green; font-weight:bold;" >The server running on "MOUSETRAP" was able to receive your request.</p></BODY></HTML>
9999/tcp open abyss?
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9099-TCP:V=7.80%I=7%D=3/30%Time=67E9B242%P=x86_64-pc-linux-gnu%r(Ge
SF:tRequest,1A7,"HTTP/1\.0\x20200\x20OK\x20\r\nServer:\x20Mobile\x20Mouse\
SF:x20Server\x20\r\nContent-Type:\x20text/html\x20\r\nContent-Length:\x203
SF:26\r\n\r\n<HTML><HEAD><TITLE>Success!</TITLE><meta\x20name=\"viewport\"
SF:\x20content=\"width=device-width,user-scalable=no\"\x20/></HEAD><BODY\x
SF:20BGCOLOR=#000000><br><br><p\x20style=\"font:12pt\x20arial,geneva,sans-
SF:serif;\x20text-align:center;\x20color:green;\x20font-weight:bold;\"\x20
SF:>The\x20server\x20running\x20on\x20\"MOUSETRAP\"\x20was\x20able\x20to\x
SF:20receive\x20your\x20request\.</p></BODY></HTML>\r\n")%r(FourOhFourRequ
SF:est,1A7,"HTTP/1\.0\x20200\x20OK\x20\r\nServer:\x20Mobile\x20Mouse\x20Se
SF:rver\x20\r\nContent-Type:\x20text/html\x20\r\nContent-Length:\x20326\r\
SF:n\r\n<HTML><HEAD><TITLE>Success!</TITLE><meta\x20name=\"viewport\"\x20c
SF:ontent=\"width=device-width,user-scalable=no\"\x20/></HEAD><BODY\x20BGC
SF:OLOR=#000000><br><br><p\x20style=\"font:12pt\x20arial,geneva,sans-serif
SF:;\x20text-align:center;\x20color:green;\x20font-weight:bold;\"\x20>The\
SF:x20server\x20running\x20on\x20\"MOUSETRAP\"\x20was\x20able\x20to\x20rec
SF:eive\x20your\x20request\.</p></BODY></HTML>\r\n")%r(ms-sql-s,1A7,"HTTP/
SF:1\.0\x20200\x20OK\x20\r\nServer:\x20Mobile\x20Mouse\x20Server\x20\r\nCo
SF:ntent-Type:\x20text/html\x20\r\nContent-Length:\x20326\r\n\r\n<HTML><HE
SF:AD><TITLE>Success!</TITLE><meta\x20name=\"viewport\"\x20content=\"width
SF:=device-width,user-scalable=no\"\x20/></HEAD><BODY\x20BGCOLOR=#000000><
SF:br><br><p\x20style=\"font:12pt\x20arial,geneva,sans-serif;\x20text-alig
SF:n:center;\x20color:green;\x20font-weight:bold;\"\x20>The\x20server\x20r
SF:unning\x20on\x20\"MOUSETRAP\"\x20was\x20able\x20to\x20receive\x20your\x
SF:20request\.</p></BODY></HTML>\r\n");
MAC Address: 02:23:36:E3:FF:87 (Unknown)
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_nbstat: NetBIOS name: MOUSETRAP, NetBIOS user: <unknown>, NetBIOS MAC: 02:23:36:e3:ff:87 (unknown)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2025-03-30T21:08:26
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 201.94 seconds
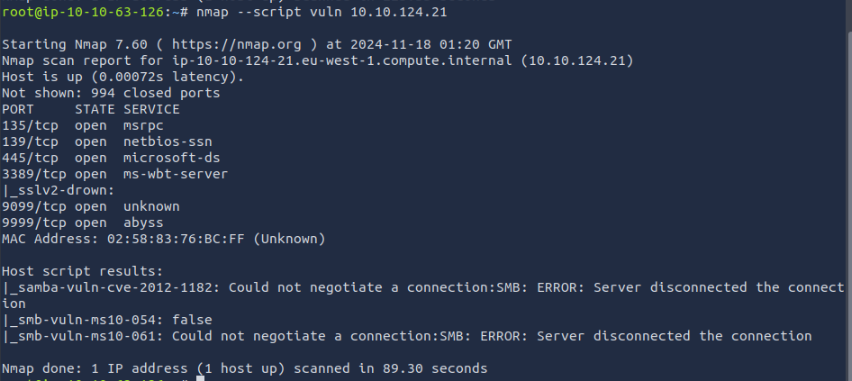
root@ip-10-10-63-126:123-135:~# nmap --script vuln 10.10.124.21162.0
root@ip-10-10-123-135:~# nmap --script vuln 10.10.162.0
Starting Nmap 7.80 ( https://nmap.org ) at 2025-03-30 22:04 BST
Nmap scan report for 10.10.162.0
Host is up (0.00025s latency).
Not shown: 994 closed ports
PORT STATE SERVICE
135/tcp open msrpc
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
139/tcp open netbios-ssn
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
445/tcp open microsoft-ds
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
3389/tcp open ms-wbt-server
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
|_sslv2-drown:
9099/tcp open unknown
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
9999/tcp open abyss
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
MAC Address: 02:23:36:E3:FF:87 (Unknown)
Host script results:
|_samba-vuln-cve-2012-1182: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: Could not negotiate a connection:SMB: Failed to receive bytes: ERROR
Nmap done: 1 IP address (1 host up) scanned in 59.82 seconds
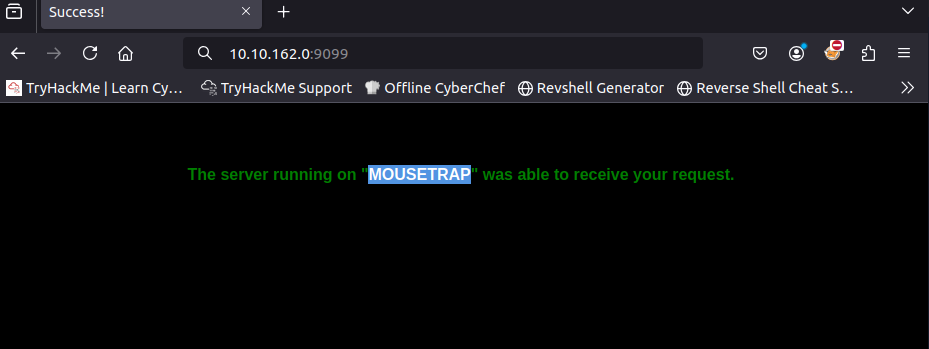
Using port 9099 in the browser